Jahaira Stoute
Contributing Writer
If you have recently received an email that says “Click here to open this message”, Do Not Click!
A phishing scam is currently targeting ESU, as of Nov. 7, 2018. This attack has already been experienced by numerous universities since early summer.
Hundreds of ESU students willingly provided their credentials and are completely unaware.
“Phishing is fooling someone into willingly providing personal information, by using deceiving tactics,” explained Alan Angulo, network administrator. “The “phisher” drops a lure waiting for a victim to bite.”
In this case, students are being fooled into providing their password.
Many students do not realize the moment they gave away their credentials.

A student will receive a reply to an email they have recently sent. The message will say:
“Unable to show this email. Click here to show full message.”
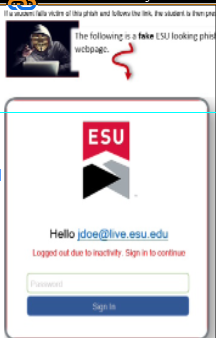
If a student follows the link, it will open a page, with an ESU Logo, appearing as if the session has timed out. It invites a student to “sign in” to continue, and so the student provides a password.
Then, the student has been sent to a random website but has also just been hacked.
If the student were to try and go back to the message and click the link again, they will find that the “sign in” interface has disappeared.
“The hackers can now log into this student’s account, and use it for exploitation purposes, like ransomware. They will also amplify the attack by replying to recent messages in the student’s inbox with the same phish technique,” explained Angulo.
Because the phishing emails are being sent from student accounts to other student accounts, it is becoming difficult to find out who has been hacked.
Also, the hackers are moving subtly to avoid exceeding the threshold, set by Microsoft that will trigger a blockage of outgoing email.
Instead, they reply to a low number of emails, like 20, expecting at least one person to click each time they phish.
Network Administration has been regularly performing “search and destroy” sessions, hunting for emails that display the links saying “Click here to show full message.”
The goal was to proactively terminate these emails before students opened them and block new ones from coming in.
However, this prompted the hackers to display a new message, in order to dodge the “search and destroy” and continue to phish.
It’s very important that the helpdesk is made aware of suspicious emails, immediately. They may say something pertinent that can be forwarded to Network Administration, and added to the “search and destroy”.
According to their reports, the number of students that clicked on this link was significantly high and becoming more difficult to contain.
“This has been the only time that the phishing campaign has been so successful at ESU. So many students were falling victims in such a short period of time, and we couldn’t understand what was happening,” said Angulo.
Angulo said the name of the Internet Service Provider (ISP) hosting the links is namecheap.com and it is based in the country of Panama. The hackers set up websites with a complex system designed to collect passwords from victims.
Some student accounts had to be disabled to stop hackers from causing further damage, however, when accounts were re-enabled, the students would go back to previous passwords.
“ESU’s firewall is protecting the students, inside our network on campus. The link gets blocked automatically by Fortigate,” explained Loedel. “However, carriers, such as AT&T, are not protected.”
Using his phone, Loedel clicked a link, while signed onto ESU’s Wi-Fi. A page popped up that said, “Webpage Blocked”. He then turned off the Wi-Fi and used data to click on another link. He was automatically taken to the fake ESU page requesting credentials.
ESU’s Computing and Communication department is working on this issue on a daily basis, including weekends and holidays.
They have also been in contact with Microsoft, who called twice during our interview, to help in dealing with this issue.
Angulo has also contacted Panama’s ISP to warn them that someone was using their internet for these purposes. He finally received a response, on Thanksgiving, stating they were suspending all the involved domains that ESU has exposed to them.
Loedel states, “Security and conveniences always go against each other. For example, in an airport, nobody likes to go through security, but it stops terrorists.”
The multifactor authentication will be an additional step to go through when logging in, but it keeps the account safer.
In a very recent communication with Angulo, he shared that ESU was able to dismantle the hacker’s infrastructure with the help of the Panama based ISP (namecheap.com). As of Nov. 30, this phishing campaign has subsided.
Please spread the word to any students who may be unaware, and change your passwords immediately just in case. Also, if you can, try to communicate with students who sent a suspicious reply to your email. Call them to let them know their account might have been hacked.
“There’s always been phishing going on since email has been around. We are hearing about it now because it’s so successful,” states Loedel. “We stop a lot but can’t stop everything; we need students’ help.”
For questions regarding this matter, please contact helpdesk@live.esu.edu
Email Jahaira at:
jstoute@live.esu.edu